Hi, what do you want to do?
Financial Times
China's internet crackdown
Beijing is plugging the last holes in its 'Great Firewall' internet censorship apparatus, hampering global groups’ ability to operate in the country.
Curated Video
The Beginners 2022 Cyber Security Awareness Training Course - Ransomware
You will be learning about all of the recent ransomware attacks you may have heard about in the news, and why they are so effective in forcing their victims to hand money over to the hackers. You will see various examples of what they...
Curated Video
Police use 'chip-off' technique to crack mobile phones
Designed to thwart encryption and passwords
Bloomberg
Anti-Ransomware Startup Halcyon Valued at $1 Billion
Cybersecurity startup Halcyon is the tech industry's latest unicorn, reaching $1 billion valuation in a deal to raise $100 million as it aims to combat the rise of ransomware attacks. Halcyon CEO Jon Miller joins Caroline Hyde to discuss...
Press Association
Technology Secretary Michelle Donelan has denied that ministers have made any concessions on end-to-end encryption
It come as the Online Safety Bill returns to the Commons for its final stages, with MPs set to consider new amendments to the long-awaited legislation.
Earlier this month saw widespread reports that the Government had...
Earlier this month saw widespread reports that the Government had...
Bloomberg
Supreme Court Will Hear Microsoft-DOJ Email-Access Fight
Oct.16 -- The U.S. Supreme Court agreed to decide whether law enforcement officials conducting a criminal investigation can demand data held overseas by Microsoft Corp. and other technology companies in a high-stakes clash over digital...
Bloomberg
Why IBM's Latest Mainframes Are a Big Deal
Jul.17 -- Caleb Barlow, IBM's vice president of threat intelligence, discusses the new IBM Z mainframes, which let customers automatically encrypt all data and applications running on the mainframes without affecting their performance....
Bloomberg
Mark Zuckerberg Is the Most Dangerous Person in the World, NYU's Galloway Says
Aug.07 -- Scott Galloway, marketing professor at New York University's Stern School of Business, comments on Facebook Inc.'s plans to merge its systems and let users exchange messages among all its different mobile apps. He speaks with...
Bloomberg
Amazon's Jassy on Customer Data and the DOJ
Oct.11 -- Andy Jassy, chief executive officer at Amazon Web Services, discusses his concerns over requests from the Department of Justice to turn over cloud data of customers. He speaks to Bloomberg's Emily Chang from the Geekwire Summit...
Bloomberg
Former NSA Director Hayden Weighs In on Encryption Debate
May 19 -- Gen. Michael Hayden, Chertoff Group principal and former NSA director, weighs in on the encryption debate. He speaks with Bloomberg's Emily Chang on "Bloomberg West." Ethan Kurzweil, a Bessemer Venture Partners partner, also...
Bloomberg
Rebuilding Instagram Chat on Facebook Technology is 'Frightening,' Says Scott Galloway
Aug.07 -- Instagram's chat is said to be rebuilt on Facebook Technology, NYU Stern School of Business Marketing Professor, Scott Galloway gives his take. He speaks with Caroline Hyde and Scarlet Fu on "Bloomberg Markets: The Close."
Massachusetts Institute of Technology
Mit: Blossoms: Fabulous Building Cryptosystems
As part of this introduction to cryptography, students will build three devices and learn how to encrypt and decrypt messages. Video is accompanied by a teacher's guide, transcript, and other handouts, as well as links for learning more...
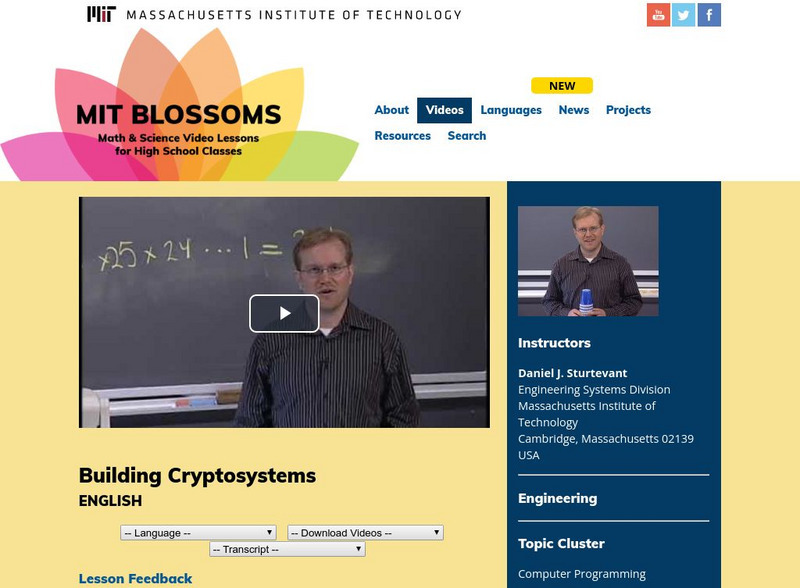
Massachusetts Institute of Technology
Mit: Blossoms: Building Cryptosystems
This video module presents an introduction to cryptography - the method of sending messages in such a way that only the intended recipients can understand them. In this very interactive lesson, students will build three different devices...
Massachusetts Institute of Technology
Mit: Blossoms: The Mathematics of Cryptography
This video lesson provides a more advanced approach to cryptography than the more experiential Sturtevant cryptography lesson also in the BLOSSOMS video library. Students will learn about the history of cryptography, and they will also...
Other
Code.org: The Internet: Encryption & Public Keys
Mia Epner, who works on security for a US national intelligence agency, explains how cryptography allows for the secure transfer of data online. This educational video explains 256-bit encryption, public and private keys, SSL & TLS...