Hi, what do you want to do?
SciShow
How Encryption Keeps Your Data Safe
Keeping our data safe and secure is necessary in today's world, but a lot of the encryption we depend on has been in development for thousands of years!
Crash Course
Cryptography: Crash Course Computer Science
Today we’re going to talk about how to keep information secret, and this isn’t a new goal. From as early as Julius Caesar’s Caesar cipher to Mary, Queen of Scots, encrypted messages to kill Queen Elizabeth in 1587, theres has long been a...
SciShow
Cryptography: The Science of Making and Breaking Codes
There are lots of different ways to encrypt a message, from early, simple ciphers to the famous Enigma machine. But it’s tough to make a code truly unbreakable.
Curated Video
What to Wear When B-Boying
Howcast - Learn what gear to wear when you're b-boying in this Howcast breakdancing tutorial with choreographer Victor "Kid Glyde" Alicea.
Curated Video
What Is a B-Boy Cipher?
Howcast - Learn what a b-boy cipher is in this Howcast breakdancing tutorial with choreographer Victor "Kid Glyde" Alicea.
Curated Video
L.A. Noire Walkthrough: "Nicholson Electroplating" (1 of 5)
Howcast - Check out part 2 of this L.A. Noire walkthrough and beat "Nicholson Electroplating" with this online demo.
Curated Video
How to Freestyle in B-Boying
Howcast - Learn how to b-boy freestyle in this Howcast breakdancing tutorial with choreographer Victor "Kid Glyde" Alicea.
Curated Video
Neo4j in 100 Seconds
Neo4j is a native graph database designed to handle highly complex relational data.
Curated Video
Introduction to IT and Cybersecurity: Cyber Security Essentials
Part 13/16 of Introduction to IT and Cybersecurity series: The video discusses the essentials of cyber security and covers various aspects such as encryption, firewalls, digital certificates and signatures, passwords, and intrusion...
Physics Girl
Quantum Cryptography Explained
With recent high-profile security decryption cases, encryption is more important than ever. Much of your browser usage and your smartphone data is encrypted. But what does that process actually entail? And when computers get smarter and...
PBS
What's In the Backpack?
A Beat Making Lab is an electronic music studio small enough to fit in a backpack. We build Labs in collaboration with communities all around the world; donating laptops, microphones, software and other equipment. From our first Beat...
Curated Video
SSL Complete Guide 2021: HTTP to HTTPS - Overview of Cipher Suites
In this video, we'll take a quick overview of cipher suites.<br/<br/>>
This clip is from the chapter "SSL, TLS, and HTTPS" of the series "SSL Complete Guide 2021: HTTP to HTTPS".In this section, we'll learn about SSL, TLS, and HTTPS.
This clip is from the chapter "SSL, TLS, and HTTPS" of the series "SSL Complete Guide 2021: HTTP to HTTPS".In this section, we'll learn about SSL, TLS, and HTTPS.
Curated Video
Python - Object-Oriented Programming - Assignment 4
In this assignment, you will learn to define a text encryption method called Caesar cypher.
<
br/>
This clip is from the chapter "Magic Functions" of the series "Python - Object-Oriented Programming".This section demonstrates the...
<
br/>
This clip is from the chapter "Magic Functions" of the series "Python - Object-Oriented Programming".This section demonstrates the...
Code.org
The Internet: Encryption and Public Keys
We can partially thank Caesar that our e-mails are secure! Viewers learn how encryption and public key cryptography keep our communications safe over the Internet. The video also briefly covers the history of ciphers, such as the Caesar...
Crash Course
Cryptography: Crash Course Computer Science #33
Uncover key concepts in cryptography in the 33rd installment of a computer science series. An engaging video describes various encryption methods. It explains substitution ciphers, permutation ciphers, the Enigma machine, advanced...
Crash Course
Alan Turing: Crash Course Computer Science #15
Meet the man many consider to be the father of computer science. Future computer scientists watch a video to learn about Alan Turing. From Turing machines to artificial intelligence, the video briefly covers his achievements.
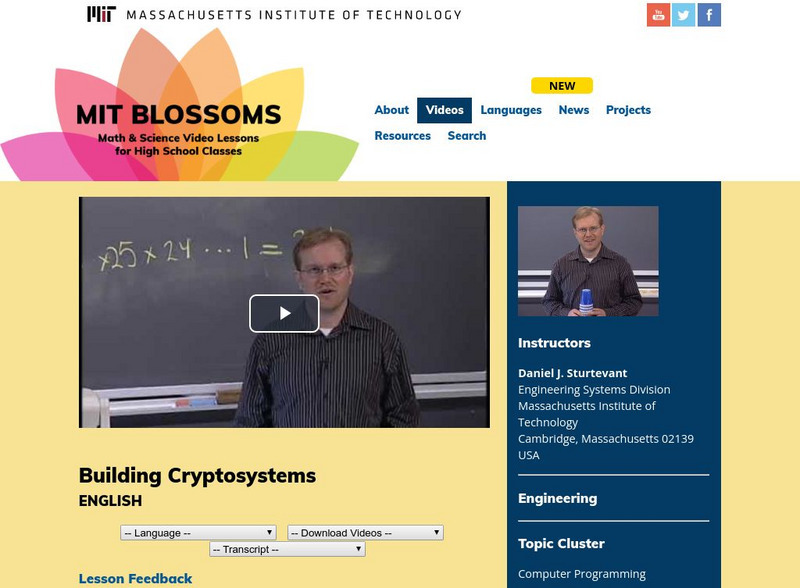
Massachusetts Institute of Technology
Mit: Blossoms: Fabulous Building Cryptosystems
As part of this introduction to cryptography, students will build three devices and learn how to encrypt and decrypt messages. Video is accompanied by a teacher's guide, transcript, and other handouts, as well as links for learning more...
Khan Academy
Khan Academy: Journey Into Cryptography: Pseudorandom Number Generators
Learn about random vs. pseudorandom number generators.
Khan Academy
Khan Academy: Journey Into Cryptography: Polyalphabetic Cipher
Find out how does a codebreaker works?
Khan Academy
Khan Academy: Journey Into Cryptography: What Is Cryptography?
What is Cryptography? A story which takes us from Caesar to Claude Shannon.
Khan Academy
Khan Academy: Journey Into Cryptography: The Caesar Cipher
Lear about the Caesar Cipher with this video.